49 / 100
overall maturity score
In our 4th edition of our Cyber Benchmark, we can confirm that companies are experiencing the benefits of their recent cyber investments, with an overall maturity score of 49%, increasing on 3 points since 2022. We consolidated and analyzed data from over 100 organizations, representing almost 5 million users, based on a field assessment of almost 200 security measures.
Cyber Benchmark results are based on NIST Cybersecurity Framework and ISO 27001/2 international standards. We found that performance related to the NIST pillars (identify risks, protect, detect, react) is relatively homogeneous: around 50% for all themes. On the other hand, with only 43% maturity, rebuilding in the wake of an attack remains the weak link in the cybersecurity strategies of large groups and companies.
This article reveals the key findings of the Cyber Benchmark, with our experts’ views and opinions on what you should be focusing on when it comes to cyber security.
Cybersecurity Maturity Live: Turning market insights into practical advice
Do you wonder how your cyber practices compare to your market? Then you might be interested in this replay! In Cybersecurity Maturity Live, Matthieu Garin, Roxane Bohin and Tilly Sonoiki dissect industry trends and explore practical advice that will empower you to protect against evolving threats.
Relive the Cyber Benchmark results – live!
The Cyber Landscape
While cyber attacks are on the rise (crime, hacktivism, countries) in a troubled geopolitical context, companies are challenged to accelerate their digital transformation. But are they really equipped to face these threats? What are the most mature sectors when it comes to cybersecurity? What assets do large organizations have at their disposal, and what pitfalls should they beware of?
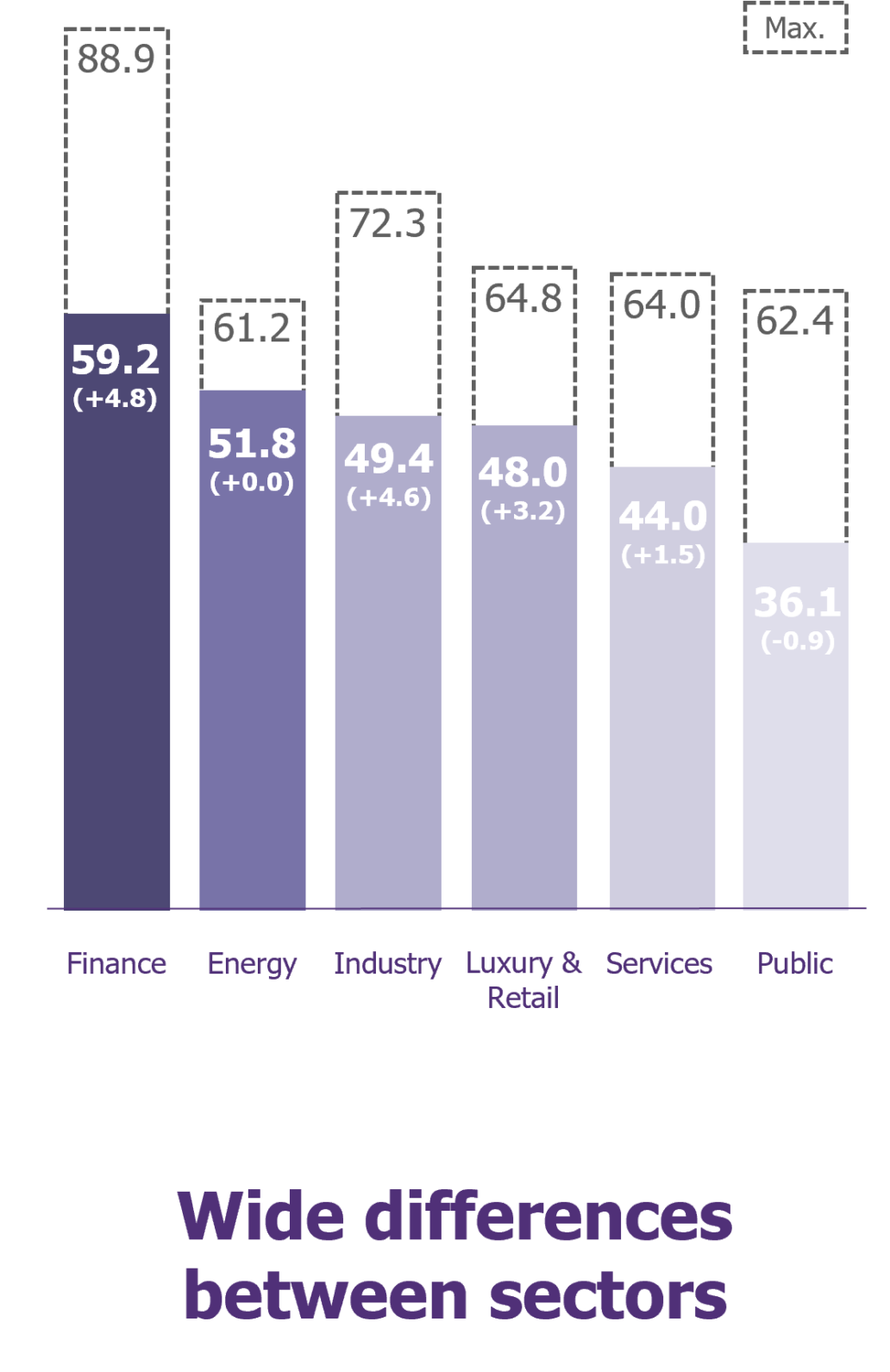
Cyber maturity in progress, yet strong sectoral disparities
The overall security score of 49% disguises significant gaps between sectors. Finance is strong with a score of 59.2% (+4.8 points from 2022). This is the result of historically high investments in the industry, encouraged by regulations (DORA, NIS2, CRA). Industry is also improving (+4.6 points), in an effort to catch up. Services (44%) and Public Sector (36.1%) have the lowest score. Although aware of the risks, this sector struggles to secure the necessary funding.
Workforce: The trump card of cyber strategies
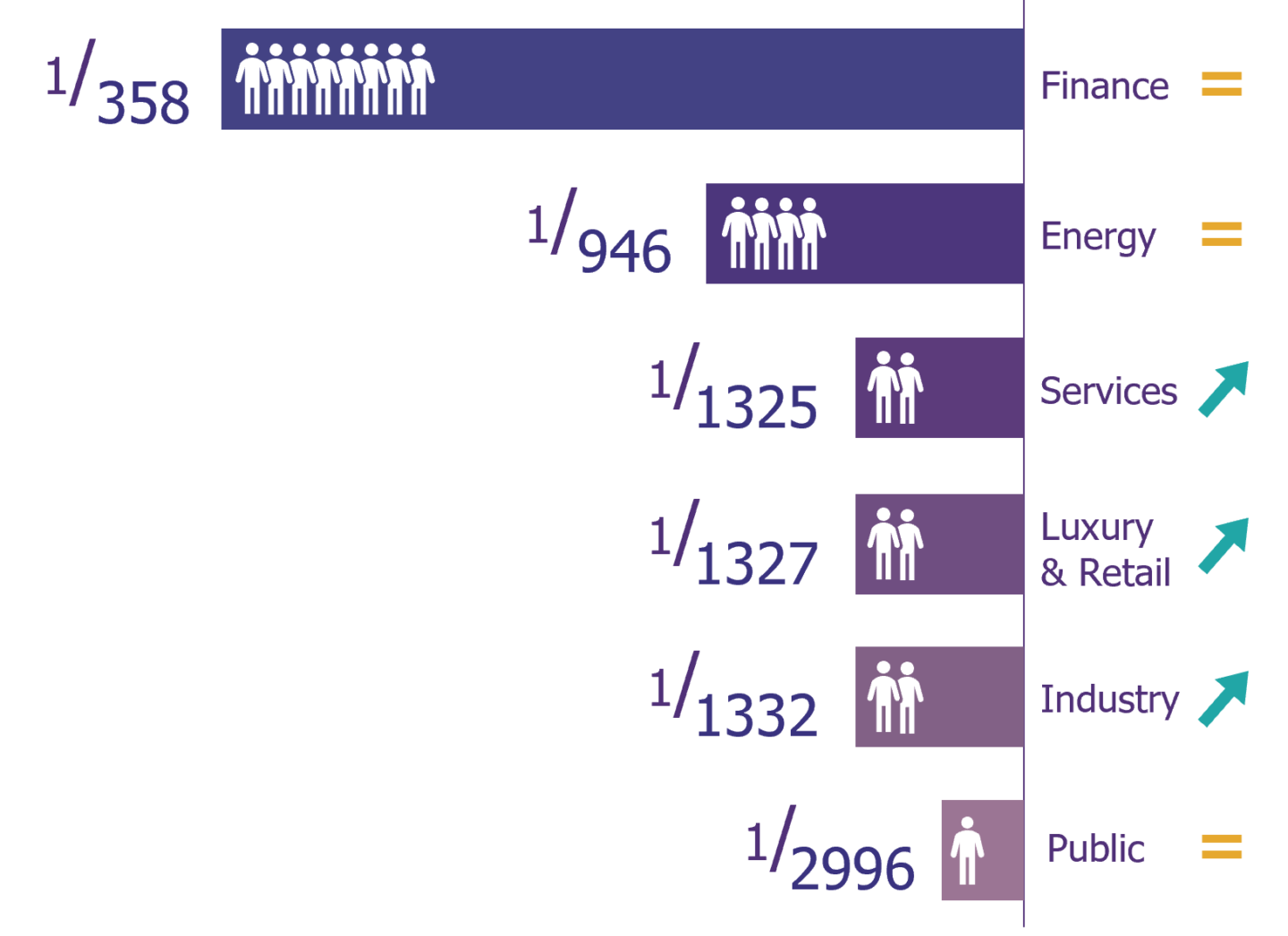
Within benchmarked organizations, security teams continue to grow: there is approximately 1 person dedicated to cybersecurity for every 1,300 employees, an increase of 11% compared to last year. However, this number is still too low in respect to upcoming challenges. Some players attempt to deal with the subject head-on, in particular through “talent management programs“.
Looking at the specifics of each sector, we believe that a plateau has been reached in Finance.
Investments: The end of a cycle
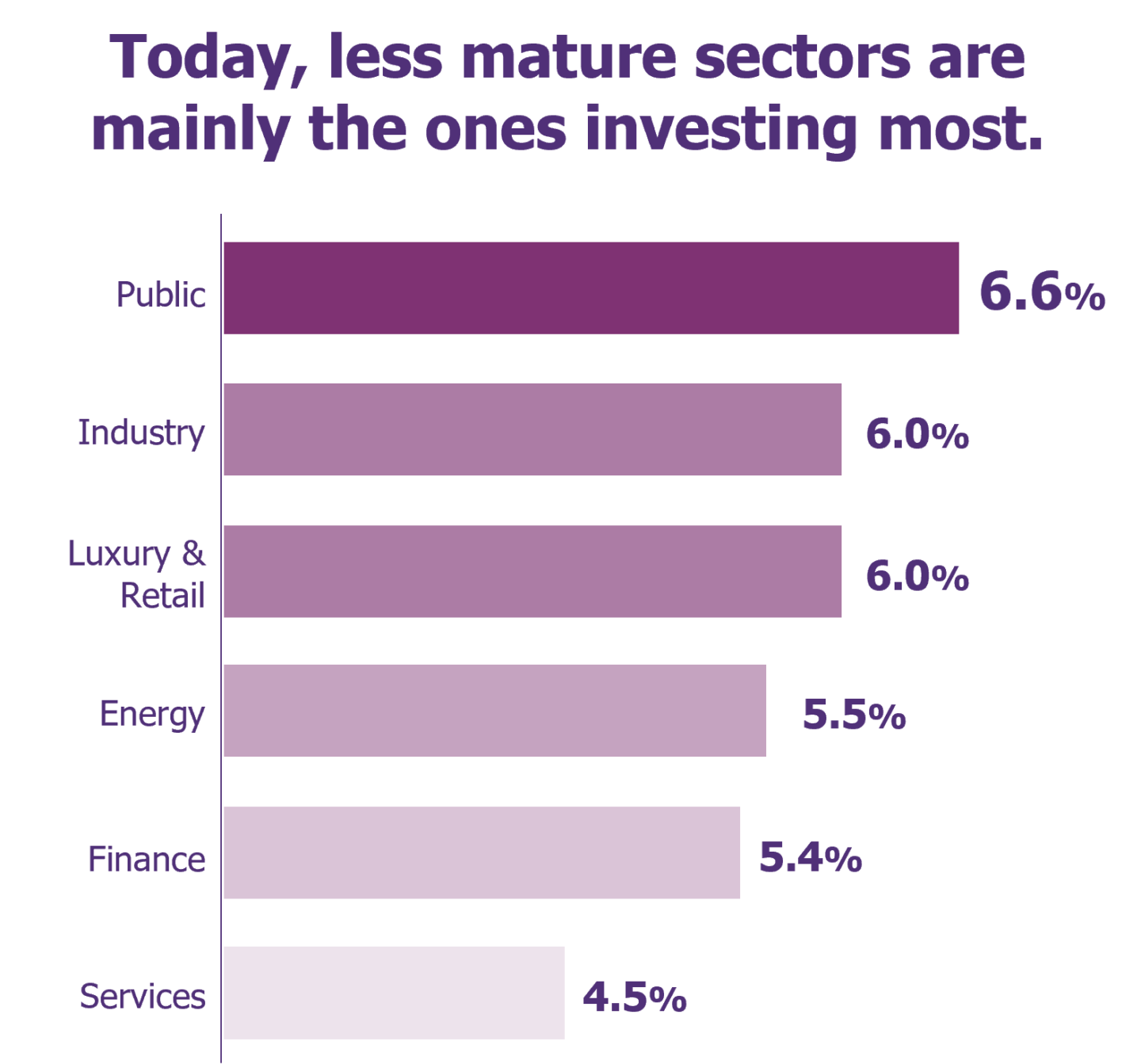
In audited companies, 5.6% of the overall IT budget is dedicated to digital security. Rather steady, this figure points towards the end of a period of strong funding.
From a sectoral point of view, the highest spending is in Public Services (6.6%), Industry (6%) and Luxury & Retail (6%). This may be explained by a longer delay in catching up, coupled with increased awareness that is now bearing fruit.
Ransomware vs. new cyber strategies: a close game
23%
of organizations
are at risk from ransomware.
In the cat-and-mouse race, are companies gaining momentum against ransomware?
The answer is yes. In 2022, when faced with the risk of ransomware attacks, 30% of organizations were in a critical situation; compared to only 23% in 2023. This reflects significant efforts on killchain topics: attack entry point (+3 points), infrastructure (+4 points), detection (+6 points) and crisis management (+3 points).
This improvement is visible in the field, where large structures are less affected by visible incidents. In reality, attacks are still being attempted, but are detected and stopped before causing too much damage.
Better, faster incident management
1 in 2 companies
deploys a "Red Button"
reaction tool
Central to response investments is a movement to review processes: 43% of organizations have formalized emergency shutdown procedures and communicate all types of incidents to their teams (versus only 23% in 2022!).
Among response tools deployed, nearly one in two companies have started to implement a Red Button-type tool to quickly isolate a portion of the network in the event of an attack.
Improved attack detection
Response strategies are enhanced by detection tools: 29% (+11 points) of organizations are continuously improving the processing and operational use of IOCs, 58% (+15 points) have detection probes connected to the SIEM, and 22% (+3 points) have begun deploying behavioral analysis probes.
Priority investments in recent years have focused on better managing attacks and reducing their operational impact.
The vulnerabilities still widely explored by cybercriminals
Cloud: better manage, monitor, detect and remediate
The Cloud is a key topic and has been the subject of significant investment. These investments are now paying off: maturity levels have reached 44.5%, compared to only 36.1% a year ago. The key findings in this space are as follows:
- The most significant progress involves Cloud administration: between 2022 and 2023, 14% of organizations have implemented multi-factor authentication (code in addition to password) or a bastion (intermediate bounce) for access to Cloud administration actions.
- When it comes to monitoring, whilst 42% of organizations relied solely on alerts from their Cloud provider in 2022, that number has dropped to 38% in 2023.
- 70% of organizations say they automatically check for cloud compliance using tools; however, only 11% automatically correct the resulting issues.
Third-party security and the expansion of interconnectivity
With a growing number of links to partners and suppliers, the issue of third-party security is increasingly challenging. The figures below have hardly changed since 2022, reflecting the complex nature of this task:
- 63% of companies include security clauses in contracts when they are signed.
- Only 37% perform regular audits of their critical IT suppliers, even though 61% have a good inventory.
- Only 13% of organizations test their response and recovery plan with their partners or suppliers on all critical perimeters.
In industrial systems, basics are mastered but considerable weaknesses remain
In the industry sector, the issue of industrial information systems security remains. With 37.6% maturity (+3.4 points), more and more historical systems designed without security by default are now opening up due to digital transformation. Efforts to implement governance (71% vs. 50% in 2022) and isolation work continue (86% vs. 78%). However, there are still significant gaps in essential security practices: perimeters are still very poorly monitored, with only 37% of companies using appropriate monitoring tools, and 42% still doing ad hoc flow filtering!
Looking ahead: Cyber trends to monitor
Until the 2024 Cyber Benchmark, here are some of the topics that should be on the minds of cybersecurity professionals in the coming months and years.
Cyber-resilience: a two-speed market
When it comes to resilience, a clear line stands between the financial sector and the rest of the industries. Yet, risks do exist and all companies are impacted.
- While 70% of financial players regularly review their residual risks in their Risk Treatment Plan (RTP), only 28% of companies in other sectors do the same.
- 60% of Finance companies continuously improve their processes for managing security incidents and have distinct cyber response plans for different scenarios. That’s only 40% in the rest of the business sectors.
- When it comes to third-party security, 60% of Finance companies have a process in place to regularly audit their suppliers, based on their criticality – compared to only 32% for the rest of the organizations.
- Most notably, 55% of Finance organizations test all Business Continuity Plan (BCP) scenarios at least every two years (DORA regulations require this to be done annually). Only 9% of other organizations perform these tests.
Zero Trust, a strategic deployment
Zero Trust is one of the major challenges of the next few years in cybersecurity. Some figures illustrate its current application.
- 24% of companies have implemented automatic micro-segmentation based on exposure, sensitivity, environment, etc. – deployed at an average of 32%.
- 14% have integrated identity-based Zero Trust Network Access into their cloud environments – deployed 46% on average.
- 28% take into account resource sensitivity and login context and apply multi-factor authentication (MFA) with conditional access – deployed 73% on average.
- 13% have begun deploying Security Orchestration, Automation and Response (SOAR) to isolate resources upon detection of an alert – deployed 48% on average.
The coming years will be regulatory
Future regulations, in particular the implementation of the NIS2 directive (scheduled for the end of 2023 and which will have a major impact on European domestic economies), will be key to increasing overall market maturity. The trick will be to ensure that requirements are set at the right level to enable progress to be made, without setting unrealistic targets.
Cyber Benchmark methodology
Maturity levels were measured against international standards (NIST Cybersecurity Framework and ISO 27001/2). The assessment was carried out during the course of audits conducted by Wavestone consultants, mainly through interviews with security leaders of the company under review. The sample, dated April 1, 2023, includes more than 100 organizations (including a majority with more than 10,000 employees and 30 Tier 1 groups: CAC40 organizations, FTSE100 organizations, or organizations with more than 100,000 employees), i.e. nearly 5 million employees. The data from these individual assessments was then consolidated and analyzed by Wavestone’s teams.
If you would like Wavestone to conduct a benchmark on your organization, please reach out to our experts.